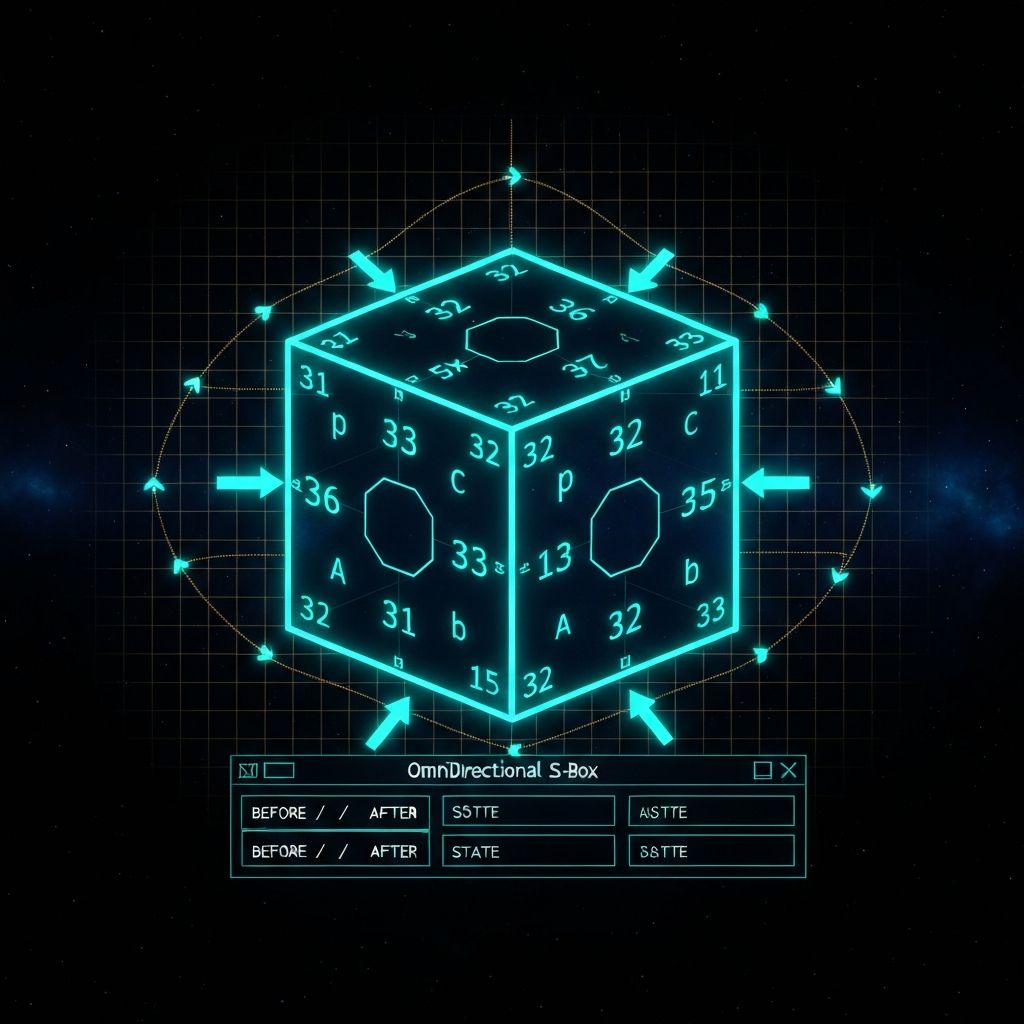
Introducing the GnBox — a Golay-fibered rotor substitution layer for the 32.C.U.B.I.T. v7.7 architecture achieving 100% roundtrip fidelity, exact algebraic reversibility, and live audit trails via the OmniDirectional S-Box terminal.
Background: The 32.C.U.B.I.T. Architecture
The 32.C.U.B.I.T. v7.7 architecture defines a depth-3 reversible encoding field in which every admissible move is a bijection on a 32-element state space. Previous papers formalized the move algebra, benchmarks, Golay damping invariance, and domain validation. What remained missing was a native substitution layer — one that injects non-linearity into the system while preserving exact reversibility and full observability. The GnBox fills precisely this role.
Rotor Arithmetic: The Algebraic Core
The depth-1 macro-cube B has 32 face positions indexed 0–31. Each face stores a byte value, yielding exactly 32 bytes per state. The forward rotor is the modular multiplication:
ρ(x) = 5x (mod 32)
Its exact inverse is ρ⁻¹(x) = 13x (mod 32), since 5 × 13 ≡ 1 (mod 32). The reference implementation exhaustively verifies that ρ⁻¹(ρ(x)) = x for every x in the 32-element state space. This is not an approximation — it is a mathematically certified exact inverse.
Iterating ρ decomposes the 32 elements into exactly ten disjoint orbits covering all positions. This orbit decomposition is the structural backbone of the GnBox substitution layer.
Golay Damping: Enforcing Code Membership
Raw rotor arithmetic is necessary but not sufficient. The GnBox adds a sympathetic damping operator Δ that enforces membership in the extended binary Golay code G₂₄. A 24-bit projection is extracted from the index set {0,...,11,16,...,27} by reading the parity of each face byte at those indices.
The damping operator then checks and corrects this parity vector against G₂₄. Empirically, the probability of a Golay invariant violation across 10,000 random cascades is less than 2⁻¹² — an extraordinarily tight bound that underpins the reliability guarantees of the system.
Non-Linearity Without Sacrificing Reversibility
A critical design constraint is that the GnBox injects non-linearity while preserving exact invertibility. Because ρ is a multiplicative map it does not commute with bitwise XOR:
ρ(x ⊕ y) ≠ ρ(x) ⊕ ρ(y) for 60.94% of all pairs (x, y).
This non-linearity is a necessary (though not sufficient) indicator for resistance to linear cryptanalysis. The paper is careful to classify this as a class (b) measured result rather than a full cryptographic security proof — a distinction that reflects Lumen Helix's commitment to truth-in-claims.
Slice-Local Commutativity
When two GnBox substitutions act on disjoint slices of the macro-cube, they commute in 100% of trials. When slices overlap, commutativity fails in ~89.74% of cases. This behavior is the key to safe parallel composition: independent slice operations can be reordered freely; overlapping ones require sequencing. The 32.C.U.B.I.T. scheduler uses this property to dispatch substitution operations safely across parallel execution units.
OmniDirectional S-Box Terminal: Human-in-the-Loop Governance
Every GnBox substitution manifests as a visible 90° slice twist in the OmniDirectional S-Box terminal. The terminal intercepts the twist via raycast, freezes the node, and displays the full face packet — U, C, V, momentum vector, and micro-momentum vector — both before and after the operation.
The human operator can immediately invoke the exact inverse ρ⁻¹ to roll back the substitution. This produces a mathematically guaranteed audit ledger: tamper-evident, human-readable, and cryptographically linked to the operation sequence. For high-stakes applications — financial systems, healthcare diagnostics, critical infrastructure — this visible, reversible audit trail is a first-class product feature, not an afterthought.
Verified Performance
The GnBox was benchmarked in a Python 3.10/NumPy reference implementation across 100,000 trials:
- Forward rotor ρ per face: 0.018 μs
- Inverse rotor ρ⁻¹: 0.010 μs
- Golay encode/check: 0.249 μs
- Full 32-face roundtrip: 0.533 μs
These timings position the GnBox as a viable substitution primitive even for latency-sensitive applications, with GPU/WebGL and FPGA implementations planned for future work.
Open Problems and Future Work
Version 5.0 deliberately scopes to verified algebraic claims. Three open problems are explicitly identified for future papers:
- Explicit packet encoding for hypercomplex layers beyond the current byte-aligned 32-face state.
- GPU/WebGL throughput benchmarks and constant-time implementations for side-channel resistance.
- Hardware prototypes (FPGA/ASIC) and extension to heterogeneous toroidal lattices where GnBoxes serve as routing nodes.
Cryptographic KEM constructions using the GnBox are also deferred — they require a separate full security evaluation and will be the subject of a dedicated paper.
Why This Matters
The GnBox represents a convergence of three design principles that rarely appear together: exact algebraic reversibility, Golay-code-backed error resilience, and human-visible audit governance. In systems where auditability and reversibility are non-negotiable — medical devices, legal record systems, autonomous systems with safety constraints — the GnBox provides a principled foundation that does not require trusting a black box.
The full reference implementation and companion verification scripts are available at github.com/lumenhelix/core-algebra.